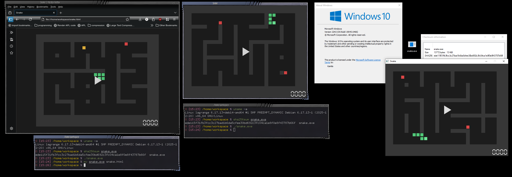
This game is a single 13 KiB file that runs on Windows, Linux and in the Browser.
(iczelia.net)
from cm0002@suppo.fi to programming@programming.dev on 12 Jan 2026 00:26
https://suppo.fi/post/9965538
from cm0002@suppo.fi to programming@programming.dev on 12 Jan 2026 00:26
https://suppo.fi/post/9965538
#programming
threaded - newest
This is pretty cool. Reminds me of .kkrieger, but this beats it in small size and that it’s a polyglot (though .kkrieger wins in visuals)
I didn’t see a link to source code for the snake tho
I’ve been looking for this game for so long! Thank you!
Edit. Here’s the source.
Oh, I meant the polyglot snake sources, but thanks
Ah whoops. Sorry about the misunderstanding
No problem :)
Upon reading my comment again, it’s a bit ambiguous. Clarified a bit
Wow, in case it’s not clear, it really is the same file for all three platforms.
Ok but is it good
VirusTotal doesn’t like it virustotal.com/…/ede115f31fb3fcc3c27bad1b6da5cfee…
Either it’s because it’s using the same technique as malware, or because it’s malware.
I’d guess the former, given it’s tiny compared to normal droppers, but you can never be sure these days.