We should all be using dependency cooldowns
(blog.yossarian.net)
from BlackEco@lemmy.blackeco.com to programming@programming.dev on 25 Nov 2025 14:01
https://lemmy.blackeco.com/post/2368195
from BlackEco@lemmy.blackeco.com to programming@programming.dev on 25 Nov 2025 14:01
https://lemmy.blackeco.com/post/2368195
#programming
threaded - newest
Been using renovate a while, 42 added this as a default!
Color me curmudgeon, but automated dependency updates should never be a consideration.
Also, one thing I do like that Github does is that it can be configured to send you a report of dependency changes (in yarn, for example).
Pinned (major.minor.patch) versions and ignore-scripts should be the default. It’s insane that the default is to execute untrusted code from the Internet.
It reminds me of back when IE would let me download a bat file and execute it
/Getoffmylawn
I mean, modern package managers generally now come with lock files, which effectively auto-pin your dependencies, until you trigger a dependency update.
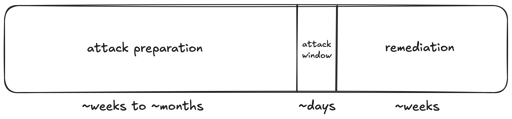
And while it isn’t bullet-proof, it does result in you effectively having a dependency cooldown most of the time. You’re only vulnerable, if you trigger the dependency update while the compromised dependency release is public.
Obviously, this can be bad enough, but it does also mean that an ecosystem with lock files is far less attractive to target with a supply-chain attack, since far fewer hosts will get compromised on average.
pnpm has minimumReleaseAge https://pnpm.io/settings#minimumreleaseage
That’s not a good idea
Most of the supply chain vulnerabilities I’ve seen published and talked about lately have been trying to do things like exfiltrate keys/secrets from developers, including ci.
So of you’ve got a pr open with the vulnerable package update on it then you’ve goofed. Even potentially without merging if you’ve not got ci set up very securely, which is probably more common than we’d like to admit